
What is Zero Trust?
Simply put, zero trust can be boiled down into the notion that everything is a threat until you can verify it isn’t: authenticate and authorise all the things, in other words. And that does mean everything, from users to devices, and everywhere, whether inside your network perimeter or not.
After all, the network perimeter increasingly doesn’t really exist, in practical terms, given the proliferation of remote working, bring-your-own-device (BYOD) usage and the cloud.
However, it’s important to understand that zero trust isn’t a security product but rather a security model. It’s a strategic thing, in other words. Nor is it a replacement for what you already have in terms of security products, but rather a mindset-shifting framework that they can work within, with some additional layers added.
Who needs to consider a zero-trust strategy?
Is zero trust something that your organisation should be considering? Ultimately, if you process sensitive data or have a hybrid workforce increasing the potential attack surface, you should at least consider the benefits of zero trust.
If your business has data and applications in the cloud, if employees access your network from mobile devices, if you want to make it harder for threat actors to compromise your systems and steal your data, then zero trust could be for you.
Why does zero trust matter?
Ask security professionals about the most common routes of entry when it comes to cyberattacks. Chances are that you’ll hear a lot about compromised user credentials as well as compromised network-connected devices.
This is hardly surprising if security controls are perimeter-based. Log in using those credentials or that device, and you are already past the security guards. That’s where zero trust comes in.
By ensuring every action – and every data or resource access request – is subject to authentication and authorisation, hurdles are erected that make it harder for attackers to succeed.
This doesn’t mean legitimate users need to be jumping them continually. single-sign-on technology can apply strong user authentication, enabling them to access multiple applications and resources as long as they have the necessary access permission to do so.
A zero-trust strategy can also make business-to-business collaboration easier without impacting security. Granular access permissions can enable business partners to access shared data, but only the data those permissions allow.
Zero trust matters because identity and access management is arguably the most important of security layers your business can employ.
How can you implement zero trust?
You can’t buy zero trust in a box. Zero trust is a strategy, not a product, so implementation will vary from organisation to organisation. However, the US-based National Institute of Standards and Technology (NIST) has seven tenets that are invaluable for anyone considering going down the zero trust route to better data security:
- All data sources and computing services are considered resources.
- All communication is secured regardless of network location.
- Access to individual enterprise resources is granted on a per-session basis.
- Access to resources is determined by dynamic policy and may include other behavioural and environmental attributes.
- The enterprise monitors and measures the integrity and security posture of all owned and associated assets.
- All resource authentication and authorisation are dynamic and strictly enforced before access is allowed.
- The enterprise collects as much information as possible about the current state of assets, network infrastructure and communications and uses it to improve its security posture.
In short, think in terms of everything being a threat until it is properly verified rather than trust being the default option. Adopt the principle of least privilege, whereby access is granted only to data and resources that are absolutely required. Enforce this with strict access controls.
Or even shorter: authorise, validate, verify everyone, everything and everywhere.
Summary
- Zero trust employs a “never trust, always verify” mantra for security.
- Think of zero trust as a strategic security framework, not as a single product.
- Zero trust can’t stop all breaches, but it can make it much harder for attackers to succeed.
- Authorise, validate, verify everyone, everything and everywhere.
NEXT UP

Tammas Ryan, Head of Customer Service at Edrolo: “The disruption caused by AI is likely to impact offshore customer service operations”
We interview Tammas Ryan, Head of Customer Service at Edrolo, a company providing teaching resources for teachers in Australia
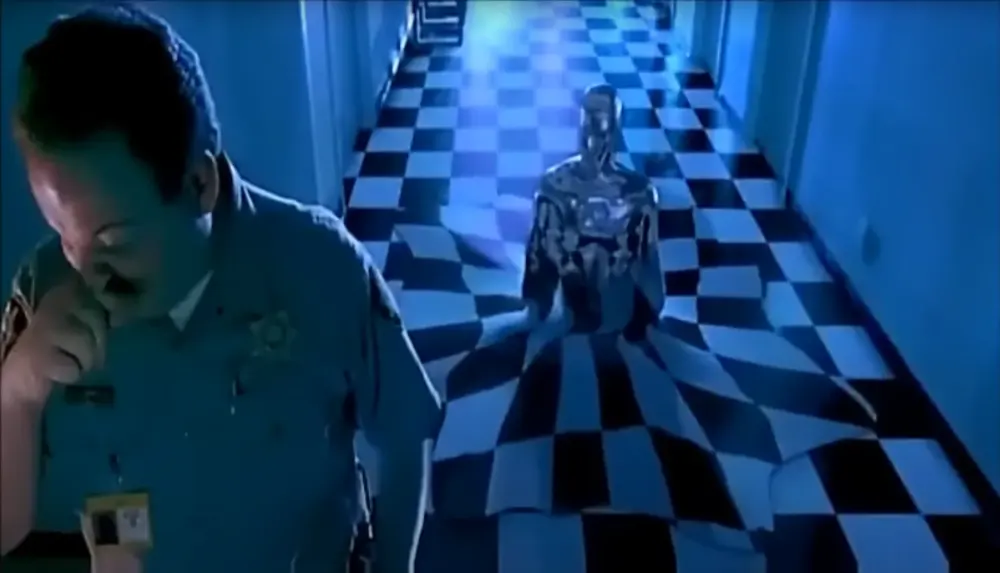
Terminator 2 in 2024: liquid metal and soft robots are here today
Metals which stay fluid at room temperature aren’t a science fiction invention. In this T2 revisit, we explore liquid metal and soft robots.

Oracle to expand cloud and AI footprint in Japan with $8 billion investment
Oracle has announced that it will invest more than $8 billion over the next decade in cloud computing and AI in Japan.