Protect
Protect is one of TechFinitive.com’s five key pillars. Here, we provide in-depth analysis of emerging threats to businesses along with a wealth of articles that will never go out of date – because the sad truth is that attackers will always be after our data.
We have a particular focus on ransomware, from simple guides to the key terms to the real-world after effects of a phishing attack. But we also want to provide practical advice on how to protect your business, whether that’s putting defensive measures in place or reminding people of the basics of cyber hygiene.
One of our key advantages is the depth and breadth of our writers’ experience. Davey Winder is one of the UK’s most respected cybersecurity journalists, having won numerous awards (it helps that he was once a hacker himself) and been covering cybersecurity ever since it became a “thing” in the 1990s.
We also draw on the knowledge that KG Orphinades earns in their day job, advising local small businesses on how to stay secure (KG also runs a website dedicated to VPNs). Last, and most definitely not least, Simon Edwards is CEO and founder of SE Labs, one of the world’s leading security testing labs, and a board member of the Anti-Malware Testing Standards Organization (AMTSO).
If you have a story that you would like to share – and we are happy to keep company names anonymous – then email us at [email protected], follow us on Twitter or join our community on LinkedIn.

Sticky Password Company Profile
Learn all about Sticky Password, a Czech password manager that has been around since the early days of the Internet.

Top tech companies in Dublin
Dublin is recognised as one of Europe’s most attractive technology hubs. Here we highlight some of the top tech companies making their mark.

WannaCry ransomware: lessons to learn in 2023
The WannaCry attack may have taken place six years ago, but many organisations haven't learned the lessons. Davey Winder issues a timely reminder.

Will anyone trust the UK to regulate AI?
The UK is keen to lead the world on AI regulation – but does it have international support?

AI exposes your biggest security flaw: your voice
What can you do to protect yourself against AI voice cloning? We explore the different cybersecurity concerns and ways to prevent attacks.

Fighting fake news: we need to build the tools to manage a world where AI has destroyed the truth
Think AI-generated images, words and videos are already causing problems? Just wait for the coming tsunami. We need tools that fight back, argues James O'Malley.

Forgetful Browsing – Brave gives website owners a new headache
What is Forgetful Browsing and how will it affect users and website owners? Barry Collins, who remembers everything, reveals exactly what you need to know.

Top tech companies in Barcelona
Barcelona has an entire district dedicated to supporting tech development, so we had plenty of choice when picking out the top tech companies in the city.
What is an Advanced Persistent Threat (APT)?
As security expert Davey Winder explains, all sizes of business – and every individual who works for them – can be a target of an APT attack. Even if the end goal is a much bigger fish.

Uniting Diverse Brands Under A Single Identity Management Solution
Read this case study on why DCC chose Okta to maximise the potential of its merger and acquisition campaigns.

Okta for Mergers and Acquisitions White Paper
Read the Okta for M&A whitepaper now to explore the key challenges businesses face during mergers and acquisitions.

Increasing Agility for Mergers and Acquisitions
Read the Increasing Agility for Mergers and Acquisitions solution brief by Okta to explore the common barriers that slow down M&A success.
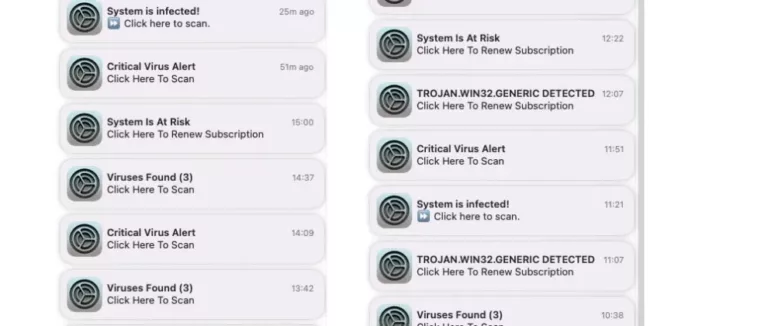
Why am I getting virus notifications on my Mac?
Are you seeing a long list of virus notifications on your Mac? Find out if you're in trouble and how you can get rid of the notifications here
How ransomware attacks work
One of the UK's leading security experts reveals how attackers break in to business networks and extort ransoms from their victims. And you can't breathe easy afterwards, as they will likely attack again.

What is Zero Trust?
A "never trust, always verify" approach to information security has never been more important, with stolen credentials increasingly used to access networks and data. Is zero trust the answer?

How AI is helping IT managers do their jobs better right now
AI adds danger to IT managers' lives, but it can also help them through better insights, enhanced security and implementing Zero Trust policies. James Morris explains how.
Cisco signs agreement with telecom giant to expand cybersecurity services
Cisco and Norwegian telecoms giant Telenor have renewed their partnership with a focus on cybersecurity and multicloud-as-a-service

Sophos reveals how GPT can help defeat cyberattackers
Research reveals how cybersecurity defenders can use GPT-3 (and by extension GPT-4) to filter malicious activity and reduce cyber threats

How to secure your business online
There's a one in two chance that your business is an easy target for hackers. Simon Edwards, founder of one of the world's leading testing labs, explains the practical measures companies can take to tighten security.

Cybersecurity: The 2022 Board Perspective (Year in Review)
Proofpoint and Cybersecurity at MIT Sloane surveyed 600 board directors around the world. Download the report to read their findings.