
How to secure your business online
This year’s statistic is 50%. Is your business hackable? Flip a coin. There’s a 50/50 chance that it’s an easy target. Unfortunately, there’s a 90% chance that someone can break in with more than a basic effort.
In the US, only half of all businesses, large and small, take cybersecurity seriously. It’s worse in the UK where only 25% are paying attention.
The problem comes from the top: 50% of company boards don’t understand cybersecurity. This is probably why half of all businesses don’t have an IT security plan.
So it should be no surprise, then, that 50% of breaches are caused by hacking, rather than tricking users or making silly configuration mistakes. If businesses aren’t on the ball, attackers will win by doing what they’ve always done.
But I have some good news. By understanding the symptomatic failures of others, you can make your business one of the most secure in the world.
How to counter stolen ‘Logins’
Hacking can mean exploiting vulnerable software, breaking into web servers and using remote desktop software to control systems. However, half of hacking involves using stolen credentials. The bad guys don’t even need to use secret hacks like exploits to break in. They just use valid usernames and passwords. These usernames and passwords are traded online, often for as little as $1.
The obvious solution is to add a layer of security called Multi-Factor Authentication (MFA), which can be free or certainly very inexpensive. If you have to enter a code generated by a free app, or sent to you by text message, that username and password combination isn’t much use to hackers.
Not enough companies have adopted this solution with one in five hacking victims failing to use MFA.
Clearly, even companies that do use MFA aren’t immune from attack. In 2022, hackers used a tactic where they attempt to log in multiple times, causing legitimate users to receive repetitive notifications on their devices, asking for access.
Time this right (or just be lucky) and the user will click “Allow” to get some peace. Multi Factor Annoyance works and is a growing threat. To counter this, you need to raise awareness among your users. For example, share this story of the LastPass hack, where the victim was targeted in exactly this way.
Protect against ransomware
Ransomware is on the rise, at rates never seen before. In the vast majority of cases the attackers target backups. Paying is expensive and could put you at risk of legal action. Besides which, nearly a third of organisations that paid were still unable to recover their data.
Over the last year every client we’ve spoken to at SE Labs has listed ransomware as their top concern. Unlike many cyberthreats, it’s an easy concept for boards to understand. Business stops until you pay. Ransomware is far too big a topic to cover in a single sentence, and will be a focus for TechFinitive in 2023. So, follow TechFinitive on Twitter and LinkedIn to keep up to date.
Ransomware was also a big focus of the 2023 SE Labs report, which you can download for free.
Email as a target
Email remains a primary attack vector. Phishing attacks over email power 20% of all successful breaches. Business email compromise (BEC) attacks, where attackers log into real accounts and send fraudulent emails, are common. In nearly half of the cases, they abuse stolen credentials.
The good news is that your employees are mostly trustworthy. 75% of breaches were executed by outsiders. While the insider threat exists, it’s not as common as some believe.
Partner organisations, on the other hand, are a more significant risk. Supply chain attacks can have much wider-reaching impacts than other types because they can affect larger numbers of targets.
Find out how to guard against BEC attacks (and why small businesses should be worried).
Legitimate code
While social engineering is popular with attackers, malware remains a significant problem. At least one-third of all breaches involve the use of malicious code. Hackers don’t need to create their own tools though. They are increasingly abusing legitimate software available on the network. Scripting systems like PowerShell can help the bad guys as much as real systems administrators.
It’s impossible to fully guard against this (as is true for any protection against attackers), but keeping software patched and up to date is a great first step. But hopefully, that’s already part of your IT security plan (which, remember, one in two companies don’t have).
Fighting zero-day exploits
Hackers still exploit vulnerabilities in software, but that’s relatively rare. Attackers used exploits in less than 10% of breaches over the last few months. However, this is an increase of 100% since last year, so I’m expecting more of this type of attack in the near future, particularly during times of international conflict. Relatively rare, ‘unknown’ zero-day exploits became more commonly used during the Russian invasion of Ukraine.
Zero-day exploits have always been expensive and, therefore, uncommon. Known only to the researchers who discovered them, and a restricted number of associates, they are mainly used by nation-states that can either afford to run their own research or pay for their exclusive use.
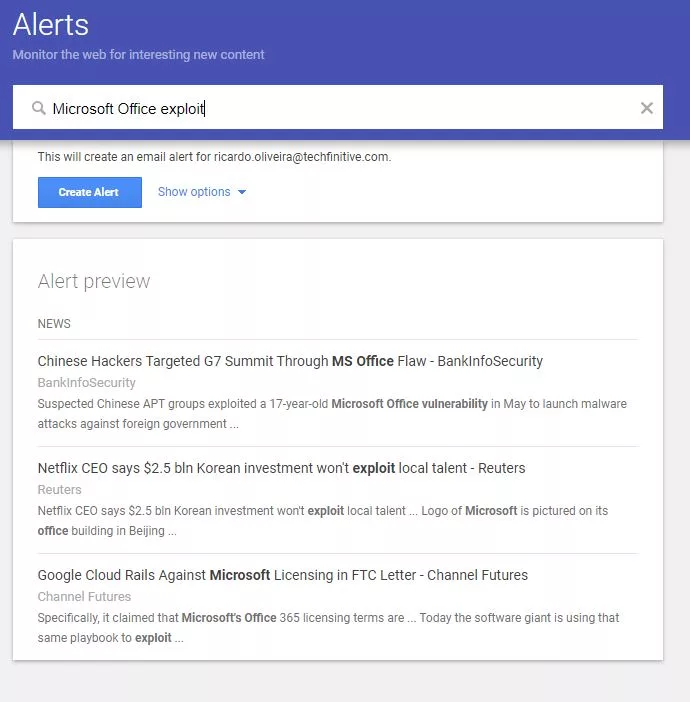
Your best defence is to stay informed. One method is to set up Google alerts for the key software you use in your business; “Microsoft Office exploit” for example.
Are you hacked already?
In 50% of cases, the attacker will let you know that you have been hacked. This could be in the form of a ransom note or a public announcement. If you keep an eye on criminal forums, such as on the so-called ‘dark web’, you might even see your data for sale.
If we go back to the start of this article, it’s not hard to realise that half of businesses aren’t paying enough attention to prevent, handle or even notice data breaches until it’s too late. And yet nothing the criminals are doing is particularly innovative.
If there is any good news, it’s that it should be relatively easy to reach the top 10% of most secure businesses in the world. The bar is so low.
NEXT UP

Tammas Ryan, Head of Customer Service at Edrolo: “The disruption caused by AI is likely to impact offshore customer service operations”
We interview Tammas Ryan, Head of Customer Service at Edrolo, a company providing teaching resources for teachers in Australia
Terminator 2 in 2024: liquid metal and soft robots are here today
Metals which stay fluid at room temperature aren’t a science fiction invention. In this T2 revisit, we explore liquid metal and soft robots.

Oracle to expand cloud and AI footprint in Japan with $8 billion investment
Oracle has announced that it will invest more than $8 billion over the next decade in cloud computing and AI in Japan.
